#Why Cybersecurity Teams Matter
Cybersecurity teams are a crucial part of any organization's risk management strategy. They are responsible for protecting the company's data, systems, and networks from cyberattacks, and they keep their team members up-to-date on the latest threats.
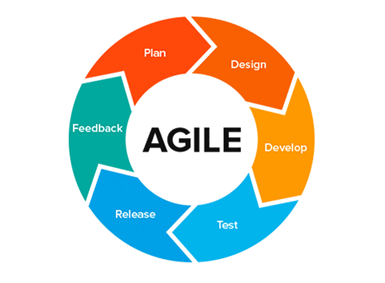
These teams are also a source of innovation and creativity within the organization when they work together in an agile environment. This allows them to respond quickly to new threats as they emerge, rather than waiting for management approval before implementing a solution.
This means that cybersecurity teams need to be agile and be able to change course quickly and efficiently when required. They also need to have a well-defined mission to know their role within the company and how their work fits into the larger picture for security across an entire organization.
#Strengthening Cybersecurity Teams in the Age of Agile
It's no secret that the cybersecurity industry is changing. The rapid rise of agile development, along with the increasingly complex nature of cyber threats and attacks, has made it necessary for organizations to adopt new methods for managing their cybersecurity teams.
Companies are doing this by encouraging their employees to work in small groups or teams. This allows them to tap into the strengths of each individual while still providing a structure for collaboration, communication, and decision-making.
The problem with this approach is that it can cause problems in terms of how you manage your cybersecurity team. When you have a group working together on a single project or task, there will always be some members who feel like they're being left out or overlooked. This can make them feel unappreciated and frustrated—and when they're frustrated, they tend to look elsewhere for solutions (which often leads them into trouble).
This is why it's important to remember that agile approaches are great for fostering creativity and innovation within your organization and are well-suited for managing cybersecurity teams effectively.
 Source: medium.com
Source: medium.com #Key Steps to Structure Your Cybersecurity Team to Work in an Agile Environment
An agile environment requires an employee who can work quickly on multiple projects simultaneously without getting lost in details. An agile environment also demands high levels of creativity, flexibility, and adaptability from employees who are constantly changing demands on them from outside sources, such as clients' or vendors' demands. Some of the key steps to structure any cybersecurity team to work in an agile environment are as follows.
#Defining your team's goals and objectives:
A company's cybersecurity team is responsible for the security agenda, which includes maintaining the security of the company's information systems, applications, and networks. The team will also monitor and analyze threats to ensure that the company's IT infrastructure remains secure. Therefore it is very necessary to define your team goals beforehand.
#Assess the roles and skills:
Assessing employees' creativity, flexibility, and adaptability of employees is very necessary as it helps to understand what type of role can be given to an individual where he/she can perform to his/her best in a flexible environment. They should be able to communicate effectively with other IT professionals to keep up with ongoing project needs or security threats that may arise within their organization's network. They must also be able to work independently for this role to be effective.
#Assigning roles to each team member:
Once the individual assessment of employees is done, the team leader and the employees themselves can easily assign new roles and positions according to their creativity, flexibility, and adaptability levels. This ensures that the team is well-balanced and can work well in any situation.
#Determine How You Will Train Your People
The type of training you provide to your cybersecurity personnel will depend on the job they are tasked with doing. If your cybersecurity personnel are responsible for protecting a network, they will need to understand how networks work thoroughly. They will also need to know how to identify and respond to any threats that come their way.
However, if your cybersecurity personnel are responsible for monitoring a network, then they should not need any knowledge about how networks work. Instead, they should be able to use a variety of tools and techniques to find vulnerabilities in the network and patch them.
#Determine How You Will Manage Their Workload
The first step in managing a team's workload is to plan how you will manage their tasks. In an agile environment, this is done by assigning tasks to each member of the team and then measuring the results of those tasks. This allows you to identify which members need more time on the task and can assign them additional work.
If any employee is unable to be physically present in the office or if you find a suitable employee who can work remotely, you can choose between some trusted VPNs to create a tunnel network between you and him. This way, the security is maintained, all while creating an agile environment for your employees.
The main goal of workload management is to eliminate bottlenecks in your organization and ensure that your team can meet deadlines. You need to be able to anticipate what will be needed and when so that you can assign tasks accordingly.
#Designate a Supervisor for each Project
The project supervisor is responsible for ensuring that all project work is completed and all deadlines are met. He/She should be someone who can lead a team and make sure all deadlines are met, as well as keep track of all tasks throughout the project.
#Understanding the Advantages of Structuring Security Teams in Agile Environments
When it comes to cyber security, it's not enough to just have an effective security strategy. You also need to be able to execute that strategy in an agile environment. That's where structuring your security teams comes in. This is done by creating a system of accountability and process that can help you focus on the right things at the right time.
The benefits of structuring your security teams in this way include the following:
- Improved communication between different departments within your organization
- Improved communication with external partners (like banks) who may have a stake in your business
- More time spent on what matters — finding and fixing vulnerabilities
- Increased efficiency and effectiveness — since you'll no longer have to waste time on things that don't matter anymore.
- It helps companies become more efficient by allowing them to identify problems early on while they are still relatively small.
#The Different Ways Organizations Structure Their Security Teams Today
As the world becomes more interconnected, so does the threat. Cyber-attacks are becoming more prevalent and sophisticated, and our ability to respond is less certain.
Organizations have been adopting different strategies to protect themselves in cyberspace and to combat this. The most common form of defense is a Cyber Defense Unit (CDU), which comprises specialists responsible for defending a company's digital assets against attacks.
"In a bureaucracy, serving the internal systems and processes takes precedence over serving customers… In Agile organizations, everyone in the organization has a clear line of sight to the ultimate customer or user and can see how work is adding value to that customer or user — or not" – Stephen Denning in Agile's Ten Implementation Challenges.
Cyberspace protection teams are another strategy that organizations can use to protect themselves against cyber threats. They typically have the same responsibilities as a CDU strategy but also work with other elements within an organization to identify threats and protect its core business operations.
#How to Make Sure Your Organization is Ready for the Future of Cybersecurity
It's not just about ensuring your organization is prepared for the future of cybersecurity—it's also about ensuring your organization has the talent and ability to take on that challenge.
Rowan Bunning, a pioneer of the agile project management approach, talked about the future of agile methodologies as:
"…the agile movement in software is part of a larger movement towards more humane and dynamic workplaces in the 21st century."
In an agile environment, you need to be able to adapt quickly. You will fall behind quickly if you aren't running in sync with your competitors. You'll find yourself falling behind even if you're doing everything right.
First, it's important to know what your organization needs. What are its goals? Is it a large corporation or a small start-up? Do you want to focus on data protection or have a more holistic approach?
Next, think about your workforce. Who are they? How old are they? Where do they work? On which platforms do they operate (mobile or desktop)? How many people use social media at work, how often and how responsibly do they do it?
Finally, how will this new strategy impact your existing security measures? Will the cost outweigh any potential benefits? Are there any potential gaps in coverage that could be exploited by hackers or cybercriminals?
These are the main things to take into account when upgrading your cybersecurity, so make sure to take your time, do research and introduce your team to the best practices when it comes to agile workflows.
This article was published in collaboration with cybernews.
∎